Latest Cybersecurity News
View all →Google can be liable for false AI Overviews, court rules
A German court has ruled that Google can be held directly responsible for defamatory claims produced by its AI Overviews. Basically, the court said that…
Cybersecurity Stars Awards 2026: Winners Announced Across 95 Categories
The Hacker NewsJun 11, 2026Cybersecurity Innovations and Excellence Most good security work is invisible by design. Today is the exception. The 2026 Cybersecurity Stars Awards…
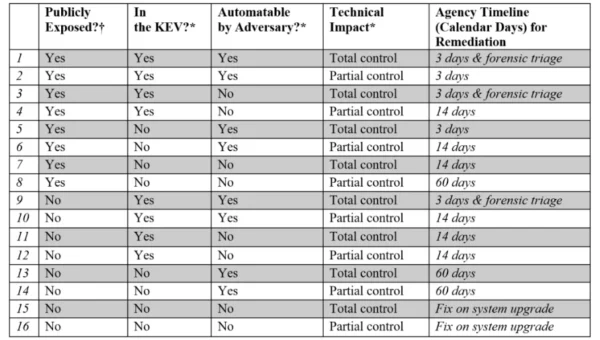
Established enterprise patching models dead in the water, says report
With Microsoft releasing its largest-ever Patch Tuesday update in June, and the continuing debate over the impact of artificial intelligence (AI) and Anthropic’s Claude Mythos…
Kmart Group to expand RFID tagging to more products and to Target
Kmart Group is set to expand its use of radiofrequency identification tags for inventory visibility beyond apparel and into other product categories, as well as…
Oracle Addresses PeopleSoft Vulnerability Amid Reports of Zero-Day Attacks
Oracle on Thursday released an out-of-band advisory addressing a PeopleSoft vulnerability that can be exploited by an unauthenticated attacker for remote code execution. The security…
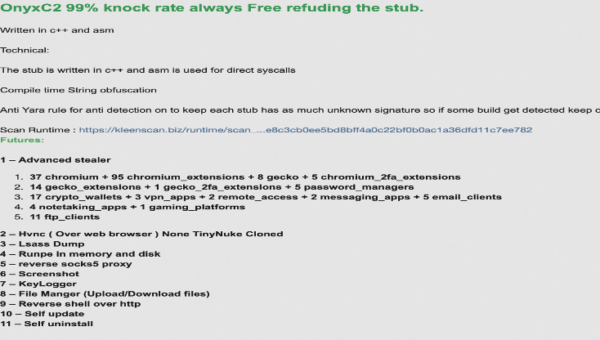
OnyxC2 Malware-as-a-Service Offers Enterprise-Grade Data Theft
OnyxC2 Malware-as-a-Service Offers Enterprise-Grade Data Theft Pierluigi Paganini June 11, 2026 OnyxC2 is a MaaS stealer targeting 210+ apps, using DLL sideloading, encrypted payloads, and…
[tl;dr sec] #332 – I’ve Joined OpenAI, fwd:cloudsec, AWS Well Architected Supply Chain Security
New Job, Who Dis? TL;DR: I’ve joined OpenAI to lead their Cyber efforts. I’m joined by Mike Aiello, an awesome security executive and human. Mike…
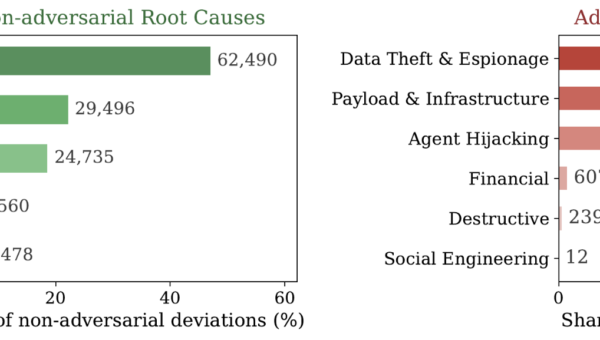
Trust No Skill: Integrity Verification for AI Agent Supply Chains
Executive Summary AI agents now extend their capabilities by installing third-party skills the way smartphones install apps. Anyone can publish a skill to a public…
ServiceNow fixes API issue after reports of suspicious tenant activity
According to the company’s advisory, the vulnerability was initially reported through ServiceNow’s bug bounty program in April, prompting an investigation and subsequent security updates. ServiceNow…






![[tl;dr sec] #332 - I've Joined OpenAI, fwd:cloudsec, AWS Well Architected Supply Chain Security](https://image.cybernoz.com/wp-content/uploads/2026/06/tldr-sec-332-Ive-Joined-OpenAI-fwdcloudsec-AWS-Well-600x340.png)